Team:Davidson-Missouri Western/Our Models
From 2008.igem.org
Krmuscalino (Talk | contribs) (→The Split Model) |
Krmuscalino (Talk | contribs) (→The Spoke Model) |
||
| Line 16: | Line 16: | ||
[[Image:spokemod.jpg|350px]] | [[Image:spokemod.jpg|350px]] | ||
| - | + | The Split Model also has a linear-type layout. There is a linear spoke for each bit of the key. | |
| + | Because every letter has the same amount of bits in binary representation as the key, the number of overall bits in the message can be evenly divided by the number of bits in the key. Instead of all the first bits of each letter XORing down the first spoke (as happens in the Split Model), the Spoke Model organizes the bits to be Xored differently. Assume that there are n bits in the entire message and x bits in the key and each character in the message. Then the first (n/x) bits are XORed down the first spoke, the second (n/x) bits XORed down the second spoke, etc. | ||
| + | Also, as opposed to a strictly linear setup, the Spoke Model reverses the flow direction of the XOR gate on alternating lines of the setup. The resulting bits at the end of each spoke, combined in order produce the Hash Output Character. | ||
| + | |||
| + | Although not a very efficient hash model in practice, this model has some interesting fractal characteristics that are interesting to explore mathematically when analyzing this model. | ||
== '''The Net Model''' == | == '''The Net Model''' == | ||
Revision as of 21:34, 29 October 2008
| Home | The Team | E. nigma Project | Parts Submitted to the Registry | Notebook |
|---|
Contents |
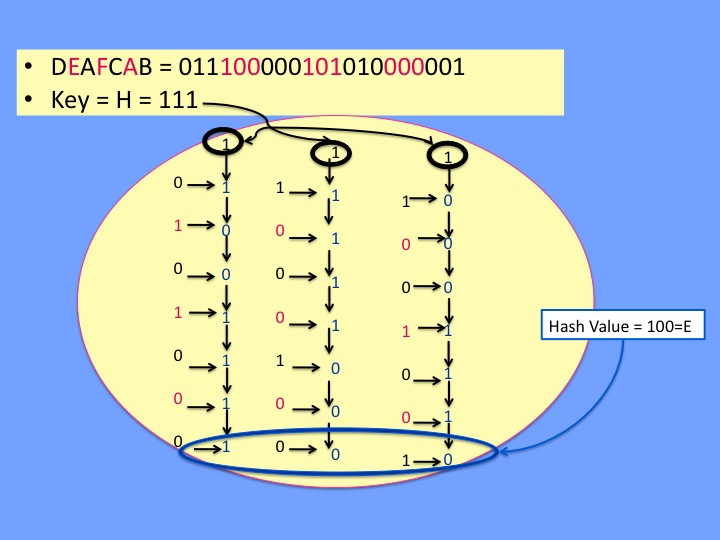
The Split Model
The Split model has a linear-type layout. There is a linear spoke for each bit of the key. Each bit of the key is XORed with the corresponding bit of the first letter of the message (converted into binary number). The result of that logic operation is itself a 1 or a 0. That number is Xored with the corresponding bit of the second letter of the message. This pattern continues until every bit of every character of the message has been XORed down the appropriate spoke. The resulting bits at the end of each spoke, combined in order produce the Hash Output Character.
This model is recommended if you're wishing to hash inputs where the probabilities of each character occurring are uniform. Therefore, for hashing aimed at password verifications, the Split model is highly recommended.
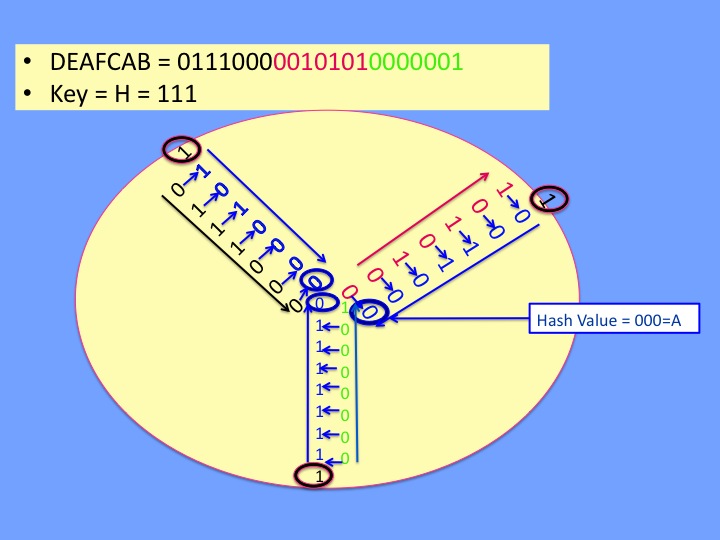
The Spoke Model
The Split Model also has a linear-type layout. There is a linear spoke for each bit of the key.
Because every letter has the same amount of bits in binary representation as the key, the number of overall bits in the message can be evenly divided by the number of bits in the key. Instead of all the first bits of each letter XORing down the first spoke (as happens in the Split Model), the Spoke Model organizes the bits to be Xored differently. Assume that there are n bits in the entire message and x bits in the key and each character in the message. Then the first (n/x) bits are XORed down the first spoke, the second (n/x) bits XORed down the second spoke, etc.
Also, as opposed to a strictly linear setup, the Spoke Model reverses the flow direction of the XOR gate on alternating lines of the setup. The resulting bits at the end of each spoke, combined in order produce the Hash Output Character.
Although not a very efficient hash model in practice, this model has some interesting fractal characteristics that are interesting to explore mathematically when analyzing this model.
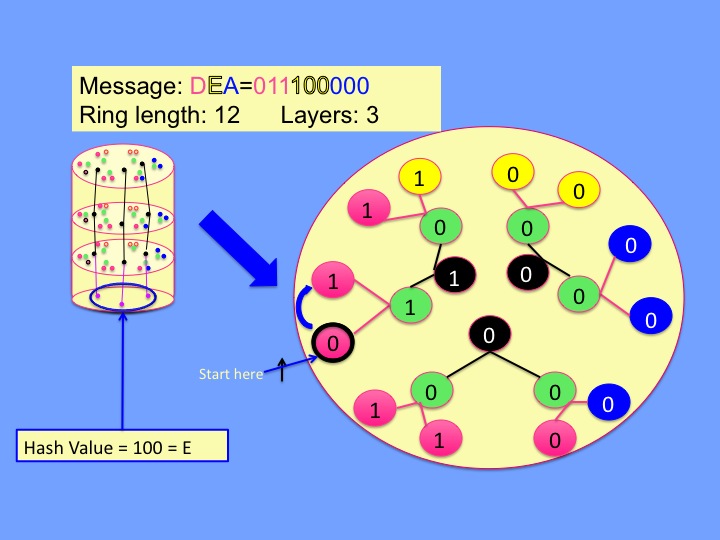
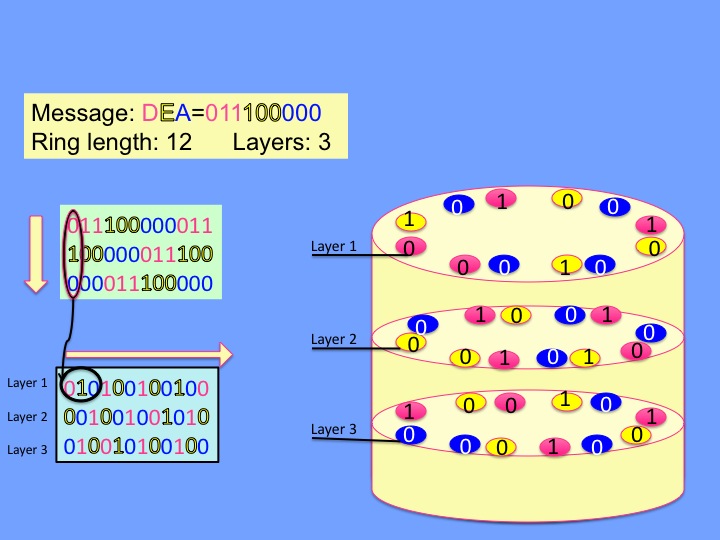
The Net Model
The Net model has a cylindrical setup in which the inputs are set up in a circular fashion. The values are hashed with their neighbor, with the final hash value resulting from the various intermediary XOR outputs trickling down the center of the cylinder. This model is more flexible than the other models in that you can manipulate the ring length(number of values on each circle). The stack size is also variable, however this has no impact on the actual efficiency of the hash model, only the ease in which the biologist implements it. This is a good model and recommened for short-length messages, specifically those less than 8 characters long. The efficiency of this model increases with the increase of the ring length, however a ring length higher than 223 is not recommended(due to time issues).
The Twist Model
The Twist model has the same cylindrical setup as the Net model, however uses a shift element to hopefully increase the efficiency of this setup and idea. The analysis of this model is still TBA.
| Home | The Team | E. nigma Project | Parts Submitted to the Registry | Notebook |
|---|
 "
"