Ideal Hash Function Characteristics
From 2008.igem.org
1)Reduces Text Down for Authentication
2) Not Reversible - From any given output, it would be virtually impossible to work backwards to get the input.
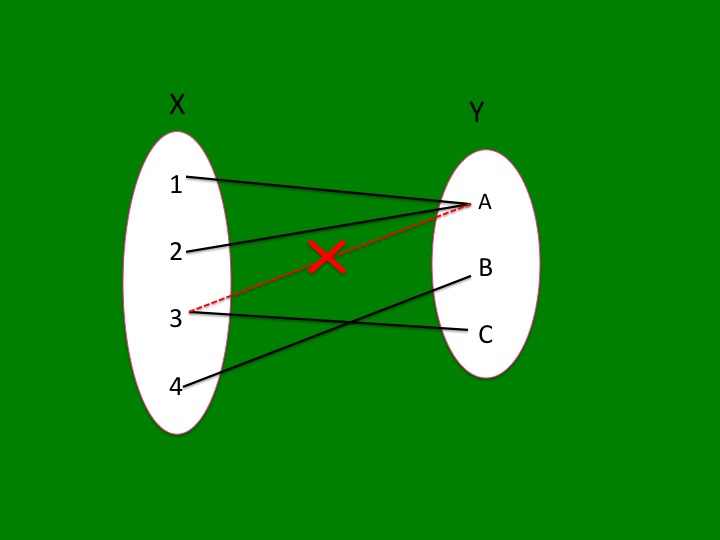
3) Each Input Has Exactly One Output - One input will always hash to the same one output.
4) Arbitrary Input Length and Fixed Output Length - Documents of unlimited length can be hashed and all documents should hash to outputs of equal (brief) length. Enables user to detect authentication quickly and ensures hash values do not give info about length of original document.
5)At Least One Collision - A collision occurs when two inputs hash to the same output. At least one collision is needed so that each input does not correspond to a unique hash output to assure the function is not reversible.
6)Minimal Collisions-Although at least one collision is needed, an ideal hash function will equally partition to all possible hash values.
7)Unpredictable Collisions-If collisions are predictable, patterns that can define the function become apparent. (only secure if it takes more than 280 attempts to deliberately create 2 colliding documents).
8)Speedy- Tags document in the split-second it's electronically transmitted (Mackenzie) Speed of Spoke Test
- [http://gcat.davidson.edu/iGEM08/cryptography_graph.pdf International Call for a Better Hash]
- [http://www.rfc-archive.org/getrfc.php?rfc=1319 Well Known Hash Function]
 "
"